The Internet
Contents
Overview
CraigNDave
https://www.youtube.com/watch?v=YLiY-nUSkuE&index=5&list=PLCiOXwirraUDvVsza-xO2mMwW9QBIa_FG
Computer Science Tutor
https://www.youtube.com/watch?v=EgvJwEKOOIg&list=PL04uZ7242_M6O_6ITD6ncf7EonVHyBeCm&index=32
What is the Internet
The Internet is an international Wide Area Network. It connects computers and networks over a large area.
The Internet originates with the U.S. government's Advanced Research Projects Agency and was used for governmental and academic communication purposes. At this stage in the development it was used to send files and emails. After the issues of connecting packet switched networks was solved, the internet took a more recognizable form. By 1983 TCP/IP protocol was created and today's internet was essentially formed.
The term 'The Internet' was adopted in 1995.
How is the Internet connected
Computer Science Tutor
https://www.youtube.com/watch?v=nRPQNaUJawE&list=PL04uZ7242_M6O_6ITD6ncf7EonVHyBeCm&index=33
Router
A Router receives packets from a host or router and uses the destination IP address that they contain to pass on the packets to another host or router.
It would be impractical to connect hosts to other hosts, which is the main reason as to why we use routers. So that many hosts can connect to the router and then the router can connect to other networks.
Gateway
A Gateway is basically Donald Trump. It controls the wall between two different systems, for example on your home router to connect from your devices to the Internet. However, unlike the Donald, Gateways can translate. They translate the current protocols for the new system to understand. This allows two different systems with different protocols to be connected. Without this, data would be kept outside the border and could not communicate across it - welcome to Trump's America.
How is data transmitted
https://www.youtube.com/watch?v=80XDMwDthuE&index=6&list=PLCiOXwirraUDvVsza-xO2mMwW9QBIa_FG
Packet Switching
Instead of having a circuit between the sender and receiver, the data transmitted is broken into small chunks (packets). Each packet is sent separately over a network on which other similar communications are happening simultaneously. The data is reconstructed on arrival.
Circuit Switching
This creates a circuit between the sender and receiver, they are connected for the duration of the transmission. This is essentially how the telephone system works. However this means that once connected neither the sender or receiver can connect or transmit to another location. It also means that if the connection is dropped then the transmission will also cease.
The End to End Principle
The devices that are communicating should be the endpoints of the communication with no external input. The Internet serves as a medium to carry traffic between them but makes no changes the data involved. Therefore the transmitting devices control every aspect of the transmission, allowing security (through encryption) and the detection of errors, which maintains the integrity of transmitted data.
Using this principle allows the Internet to easily grow because there is no direct control over the number of endpoints.
How The Internet Works
https://www.youtube.com/watch?v=5XPB4HqlFWU&list=PLCiOXwirraUDvVsza-xO2mMwW9QBIa_FG&index=7
IP Address
IPv4 is a 32 bit address that is separated into 4 bytes.
10101100 00010000 01110010 00100011
is
172 . 16 . 114 . 35
The IP address can be broken into 2 components, the Network ID (this obviously identifies the network) and the Host ID (which obviously identifies the device or host). The exact break up between the network and host ID's will depend on the class of the IP address under consideration.It also defines the possible number of networks and the number of hosts per network.
https://www.youtube.com/watch?v=xa5MXKQbfWQ&list=PLCiOXwirraUDUYF_qDYcZV8Hce8dsE_Ho&index=153
Class A / 1
Class A addresses are assigned to networks with a very large number of hosts. The high-order bit in a class A address is always set to zero. The next seven bits (completing the first octet) complete the network ID. The remaining 24 bits (the last three octets) represent the host ID. This allows for 126 networks and 16,777,214 hosts per network. Figure 1.4 illustrates the structure of class A addresses.
Class B / 2
Class B addresses are assigned to medium-sized to large-sized networks. The two high-order bits in a class B address are always set to binary 1 0. The next 14 bits (completing the first two octets) complete the network ID. The remaining 16 bits (last two octets) represent the host ID. This allows for 16,384 networks and 65,534 hosts per network. Figure 1.5 illustrates the structure of class B addresses.
Class C / 3
Class C addresses are used for small networks. The three high-order bits in a class C address are always set to binary 1 1 0. The next 21 bits (completing the first three octets) complete the network ID. The remaining 8 bits (last octet) represent the host ID. This allows for 2,097,152 networks and 254 hosts per network. Figure 1.6 illustrates the structure of class C addresses.
Table of Addresses
| Class | Value for w 1 | Network ID Portion | Host ID Portion | Available Networks | Hosts per Network |
|---|---|---|---|---|---|
| A / 1 | 1–126 | w | x.y.z | 126 | 16,777,214 |
| B / 2 | 128–191 | w.x | y.z | 16,384 | 65,534 |
| C / 3 | 192–223 | w.x.y | z | 2,097,152 | 254 |
Named Addressing
Computer Science Tutor
https://www.youtube.com/watch?v=gEjig8ylb4A&list=PL04uZ7242_M6O_6ITD6ncf7EonVHyBeCm&index=34
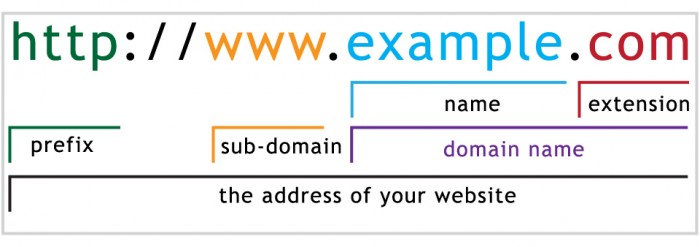
URL
The Uniform Resource Locator is the standard address used to find a page, Web server or other device on the Web or Internet.
It specifies: How to access the server, ie which protocol to use Which server to access, ie the address if server What is to be accessed on the server, ie the path on the addressed server.
This was invented so that users could use a memorable name to refer to a network and a host on that network.
Domain Name
The domain name identifies one or more IP addresses. For example, the domain name "Microsoft.com" represents about a dozen IP addresses.
Often the term 'Domain Name' is used instead of the correct term 'Full Qualified Domain Name' (FQDN), A FQDN relates to a specific host so www.microsoft.com is a FQDN.
The DNS system is a hierarchy.
Domain Name Server
A Domain Name Server accepts a Domain Name and returns the IP address associated with this Domain Name.
Your network connection settings will often specify a DNS address, or alternatively can be set to automatically set the to the default DNS for the network you are connected to. Rogue DNS servers can be set up to redirect users to alternative sites, your DNS server address could then be changed by a rogue piece of software and you may never notice. This is often called a man in the middle attack.
Internet Registrar
An organization which is capable of providing and controlling the domain of an URL is known as a registrar. They allow for the reservation of specific web addresses for anybody who wishes to purchase it, a vast majority of which are to be repaid annually or else be open to the public again.
Different domains have different costs and requirements depending on what they are, with the best examples being country-specific top-level domains such as .uk or .us
Domains that are created by and for governmental and military purposes are typically restricted from the public or are made invisible to the public altogether.
Internet Registries
Computer Science Tutor
https://www.youtube.com/watch?v=c&list=PL04uZ7242_M6O_6ITD6ncf7EonVHyBeCm&index=35
An Internet Registry holds registered domain names, according to which ones are currently in use. The registry will allow users accessing the domain name to access the linked IP address and thus the intended website.
Related Topics
You can find all of the related IP Addressing topics, such as NAT, IPv6, Port Forwarding etc below: